Installation Prerequisites
In order to use Volatility, you will need to install a few prerequisite programs and packages.
Prerequisites
- Python 2.6 or greater, but not Python 3.0 Python 2.6 will be used in this guide
- Distorm (Malware Plugins, Volshell)
- Yara (Malware Plugins)
- PyCrypto (Core)
- Subversion Client. We recommend TortoiseSVN for Windows
- 7zip or an application that can unzip zip and gzip files
- MinGW or other C Compiler (for compiling Pycrypto library)
Windows Installation
This covers how to install Volatility 1.4 on Windows.
Python Installation
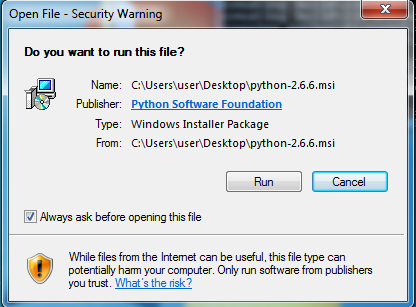
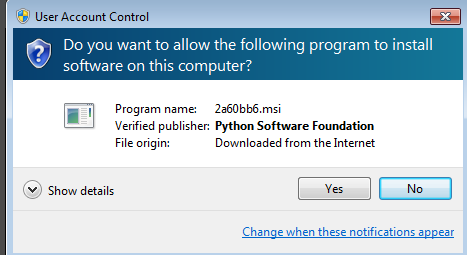
In order to use Volatility, you must first install Python. You should get version 2.6 for Windows. When you download the file, double-click to install and you will see the following security message. Just click Run.
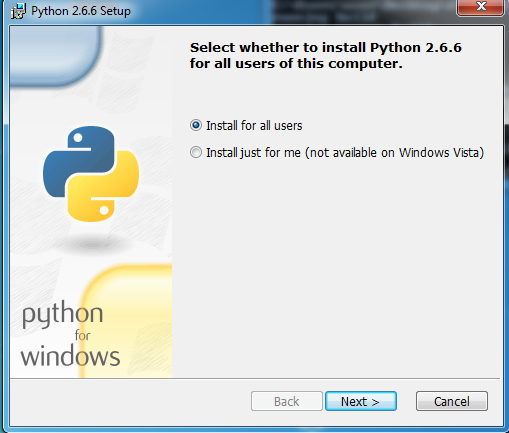
Choose the appropriate install options. Most likely you will want to install for all users on the machine:
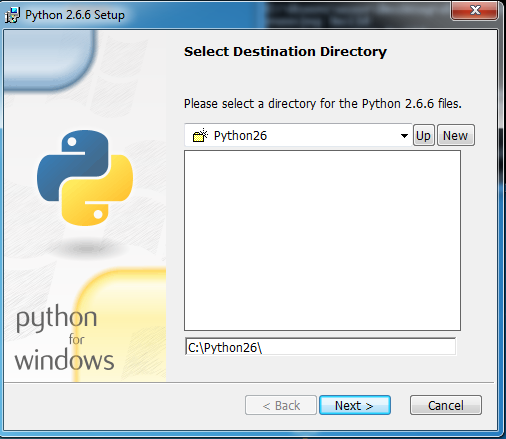
The installer will ask you where you would like to install the Python files, the default under C:\Python26 should be fine:
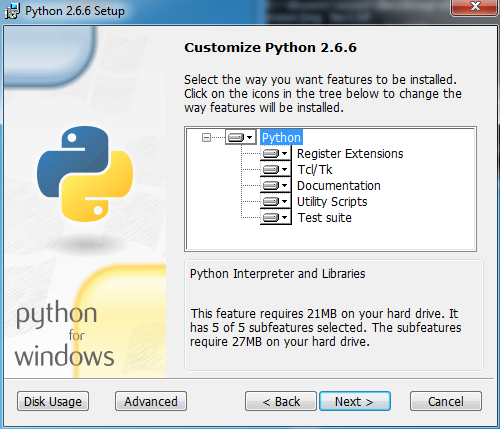
The installer will then give you the option for more advanced install options. Unless you know what you are doing, it will be best to leave all options enabled:
On Vista/Windows7 you may have to confirm that you want to install:
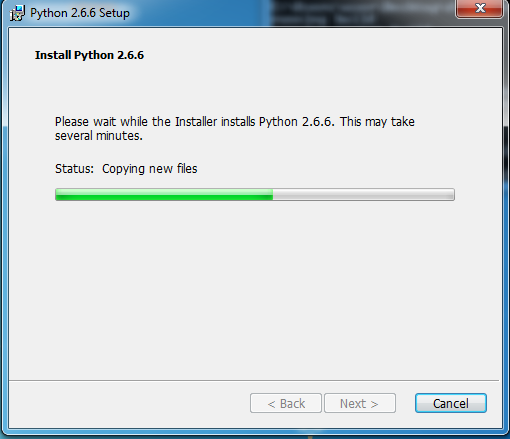
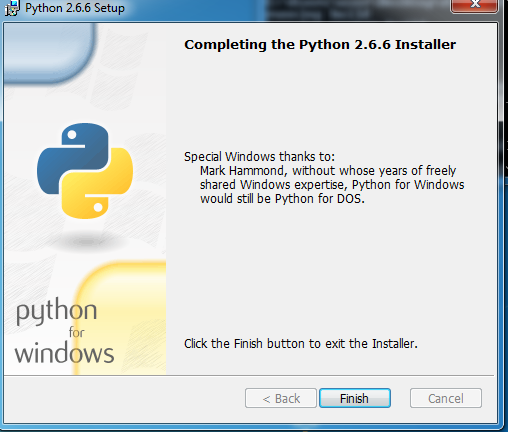
Hit “Next” and Python will now install. Hit “Finish” when installation completes:
Setting Environment Variables
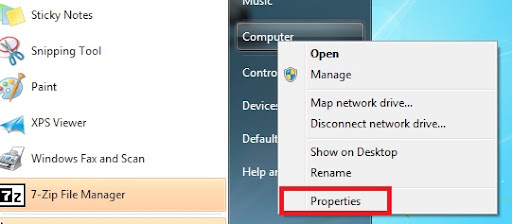
After Python is installed, you should make sure that the Python extensions are registered. If you have a regular start menu, click on start and then right click on “Computer” and choose properties. If you have the classic start menu, just right click on “My Computer” and choose properties.
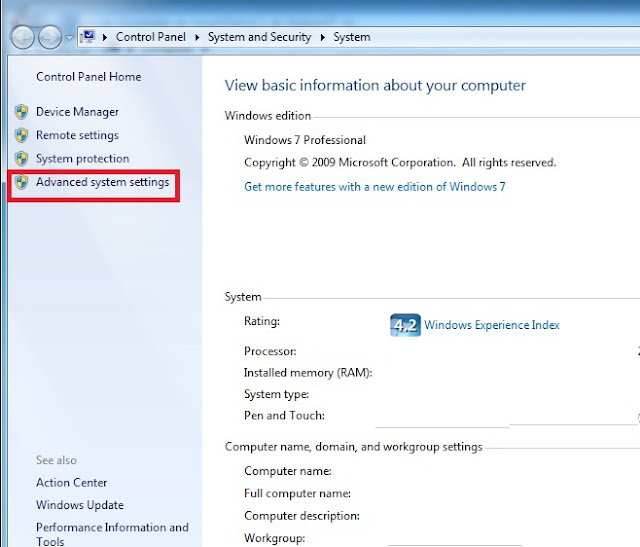
If you have Windows 7 you will see the following screen. Choose "Advanced System Settings". You should see the following (some personal details removed):
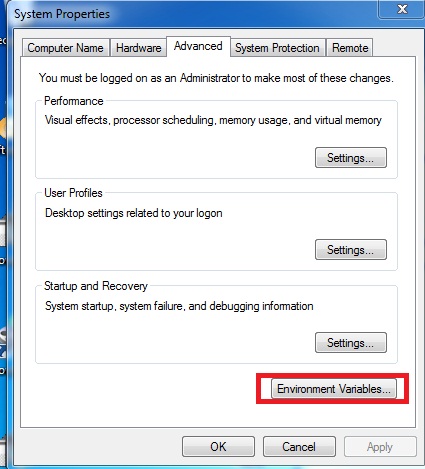
Make sure you are on the "Advanced" tab and choose "Environmental Variables":
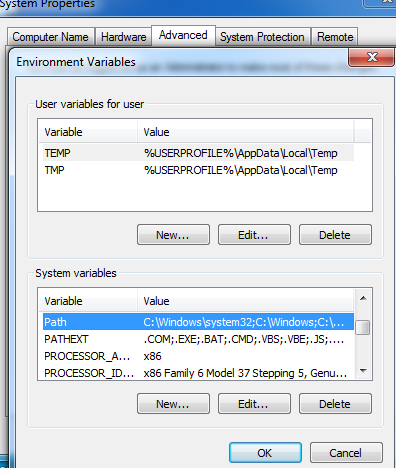
On the next screen find the "Path" variable and click "Edit":
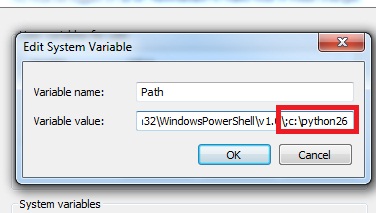
Click on the text and scroll all the way to the end. Append the path of our Python installation to the end of the existing Path variable. Where it says “Variable Value” go to the end of the line and add the following:
;C:\Python26
The semicolon separates our new Path location from the current values. If the location of your Python installation is different from the above, type the appropriate folder location instead.
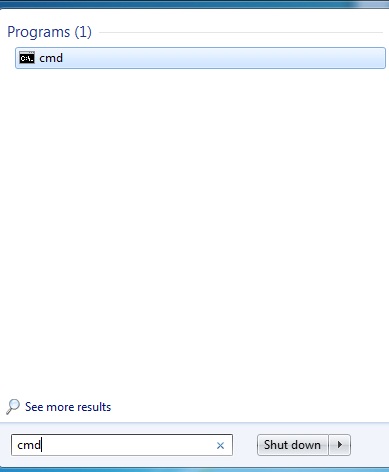
Now we are ready to test that we have set up everything correctly. Open a command prompt by clicking on the "Start Menu" and clicking on "Run". For Windows 7, click "Start" and type "cmd" in the search text box and hit "Enter":
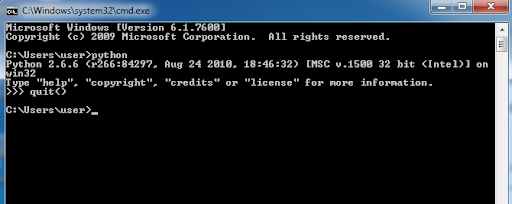
Type "python" into the command prompt. You should then see the Python header and command prompt >>> Type "quit()" to exit. If this works, Python is installed correctly.
Installing Dependencies
Installing MinGW
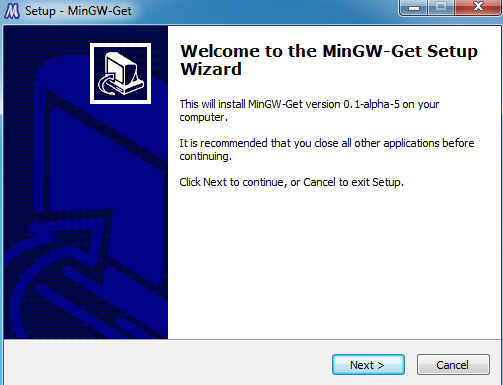
Occasionally you will need a C/C++ compiler in order to install Python libraries. If you install Distorm3 or Pycrypto from source, you will need a compiler. Download the compiler from the Sourceforge site. Make sure you get the "ming-get-inst" installer as shown below: Double click the installer. You should see the following picture. Hit Next to continue.
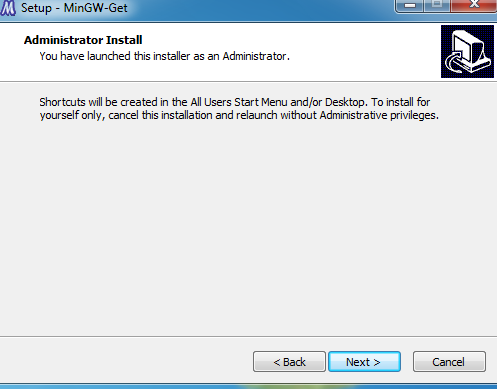
If you are running as Administrator you will see the following screen. Just hit Next.
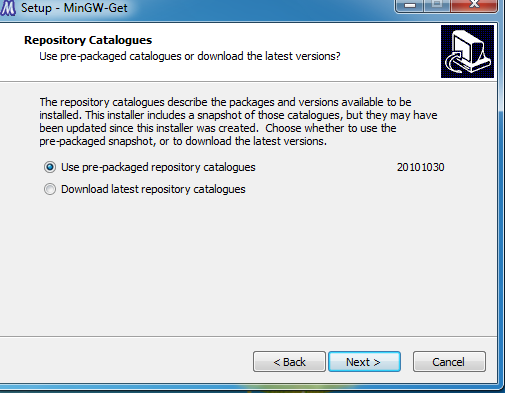
You will have a choice to install the latest MinGW build or prepackaged binaries.
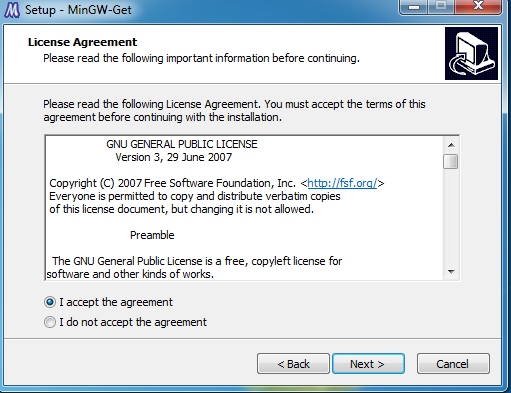
Accept the agreement.
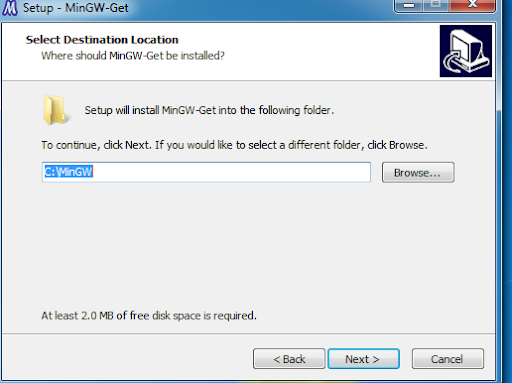
Choose a location to install MinGW.
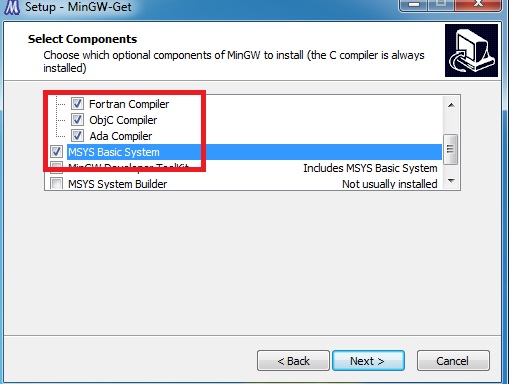
Keep accepting defaults until you get to the "Select Components" screen. Here you will need to make sure you have at least the C++ compiler checked as well as "MSYS Basic System" so you will have the "make" utility.
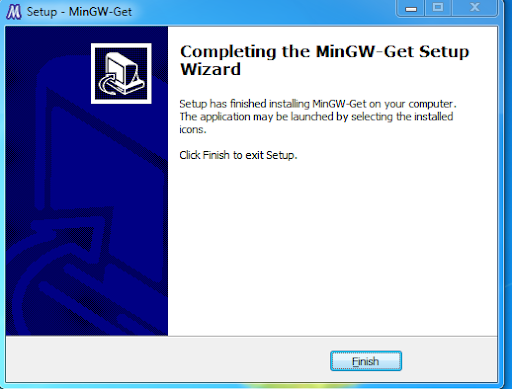
Hit Next. A black command prompt may appear as things are installing; just ignore it. If all goes well you will see the "Finish" screen. Just hit "Finish".
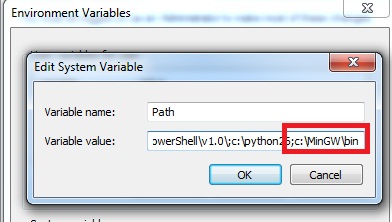
Add the "bin" directory of MinGW to your path like you did for Python. If you accepted the default installation directory the text to add would be:
;C:\MinGW\bin
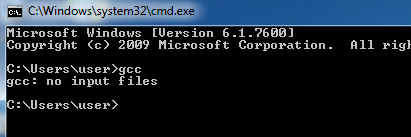
You can test that this works by typing "gcc" plus "Enter" at the command line. You should see "gcc: no input files" if your path variable is set up correctly:
Installing Pycrypto
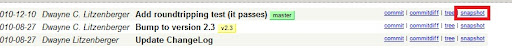
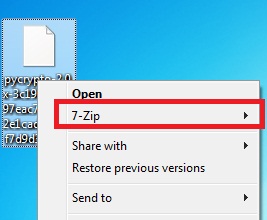
If you do not have a C compiler like MinGW installed, you can install a precompiled version of Pycrypto from www.voidspace.org.uk. If you installed MinGW as above you can install Pycrypto as follows. To install from source, first go to the Pycrypto repository page. You can download a snapshot as a gzip file: If you have 7zip installed, right click on the downloaded file and choose open 7zip->Open Archive:
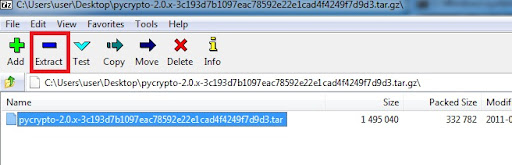
Double click the tar file inside and click the "Extract" button.
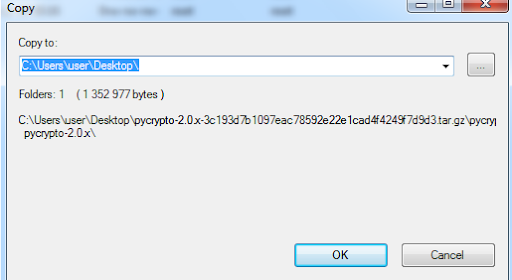
Choose a location to extract the folder to:
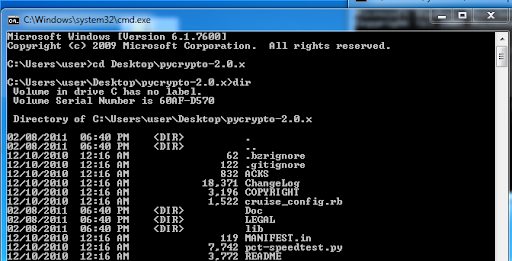
Once the folder is extracted, open the command prompt and change directory into that folder. In this case, the folder was extracted onto the Desktop, so the command issued is:
cd Desktop\pycrypto-2.0.x
Once inside you can issue a "dir" command to make sure you have all the files, including "setup.py"
Type the following commands to install (wait until the first one finishes before typing the second one):
python setup.py build -c mingw32
python setup.py install
As long as you don't see any errors Pycrypto should be installed correctly.
Installing Distorm3
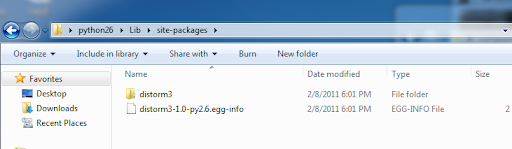
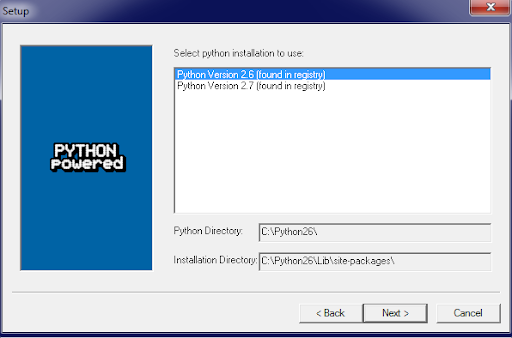
Distorm3 is used by several Malware plugins as well as the Core Volshell plugin. It's easiest to install the precompiled library for Python 2.6, which is the method shown here. Go to the Distorm Google Code page and download the distorm3-1.0.win32.zip which contains the library for Python 2.6. Unzip the file and navigate into the Python26\Lib\site-packages directory:
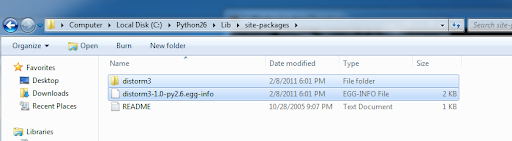
Copy all contents into your Python 2.6 library location, in this case C:\Python26\Lib\site-packages
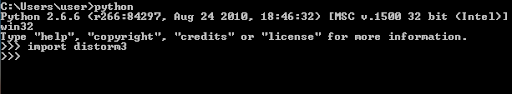
You can check the installation by running python and importing distorm3. If you don't see any errors, distorm3 was installed correctly.
Installing Yara-Python 1.4a
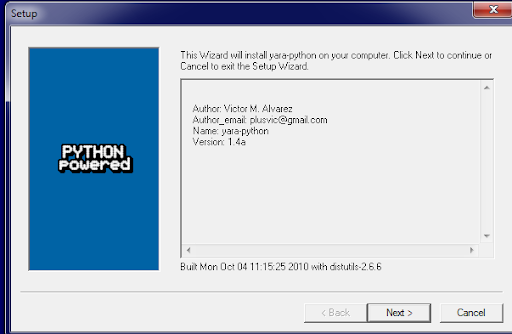
Download the appropriate yara-python-1.4a.win32-py2.X.exe Windows installer. In this guide we will use yara-python-1.4a.win32-py2.6.exe. Double click the installer and click Next. The installer should pick up your Python installation. If you have more than version of Python installed, choose the installation you will be using for Volatility.
Accept all defaults, hitting Next until complete. As long as there are no errors shown installation should be successful. You an always verify by running Python and typing "import yara"
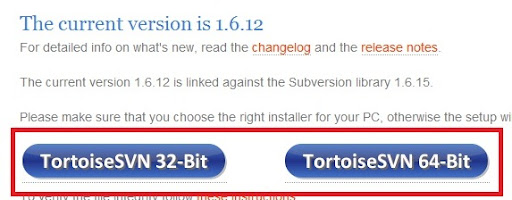
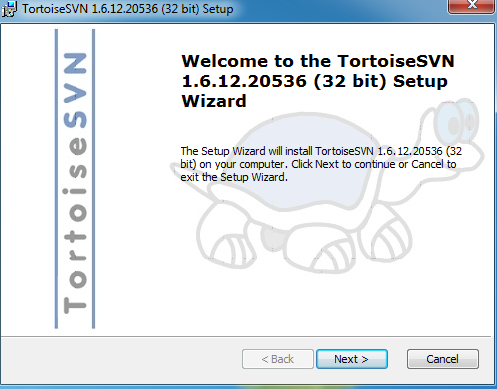
Installing TortoiseSVN
In order to get the source code for Volatility 1.4 from the repository, you will need a Subversion (SVN) client. You can download the client from http://tortoisesvn.net/downloads.html. Make sure to choose the correct installer: Double click the installer and keep hitting next. Accept all defaults and accept the user agreement. Hit "Finish" when the installation completes.
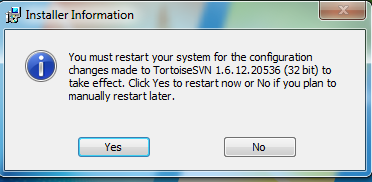
You will be asked to restart your computer after TortoiseSVN is installed.
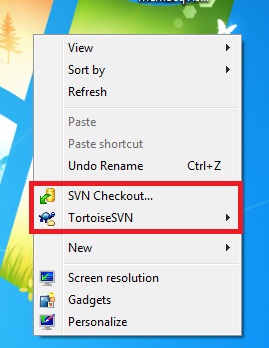
After restarting, you can verify that TortoiseSVN is installed correctly by right-clicking on the Desktop. If it is installed, you will see it in the menu:
Installing Volatility 1.4 from SVN
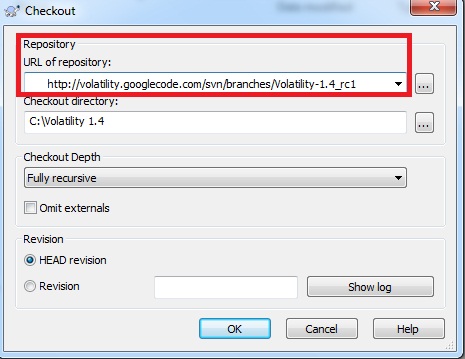
Once you have a Subversion client installed, you can download the latest source code for Volatility 1.4 from the code repository. This guide will use TortoiseSVN. First create a folder where you want to keep the Volatility source code. For this guide we will create a folder "C:\Volatility 1.4". Go inside this folder and right-click, bringing up the menu options for TortoiseSVN. Choose "SVN Checkout":
Type the following url for the repository:
http://volatility.googlecode.com/svn/branches/Volatility-1.4_rc1
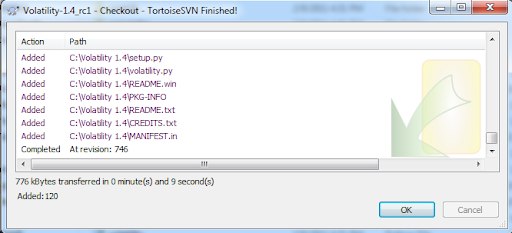
All other defaults should be fine, click OK. When the repository is finished downloading click OK to close out.
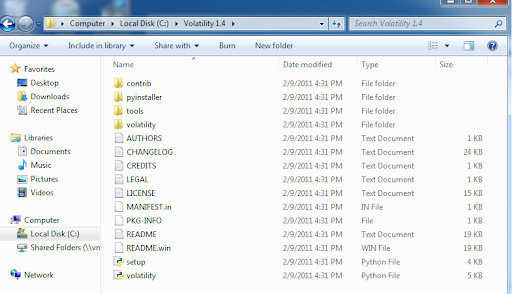
You should then see all the Volatility source code in the folder.
To use Volatility, open a command line and navigate to the Volatility source directory. In this case:
cd "c:\Volatility 1.4"
Then type:
python vol.py -h
You should see a long list of output that includes all of the plugins that are available. For more information on how to use Volatility check out BasicUsage and CommandReference.
轉自 http://code.google.com/p/volatility/wiki/FullInstallation











 將SSD拆開後,可以看到其內部是由一張電路板,上面組合多片快閃記憶體和控制晶片而成。而去除掉外殼的SSD很容易受到破壞,不論在撞擊、耐溫等層面,等同毫無保護。
將SSD拆開後,可以看到其內部是由一張電路板,上面組合多片快閃記憶體和控制晶片而成。而去除掉外殼的SSD很容易受到破壞,不論在撞擊、耐溫等層面,等同毫無保護。 


 磁力須達到一定強度等級,才有可能讓快閃記憶體產生電流,進而達到損毀的目的。
磁力須達到一定強度等級,才有可能讓快閃記憶體產生電流,進而達到損毀的目的。 由於泡水並不會破壞線路,所以資料毀損率不高。
由於泡水並不會破壞線路,所以資料毀損率不高。